· 101 min read
Indoor Climate Field Proof
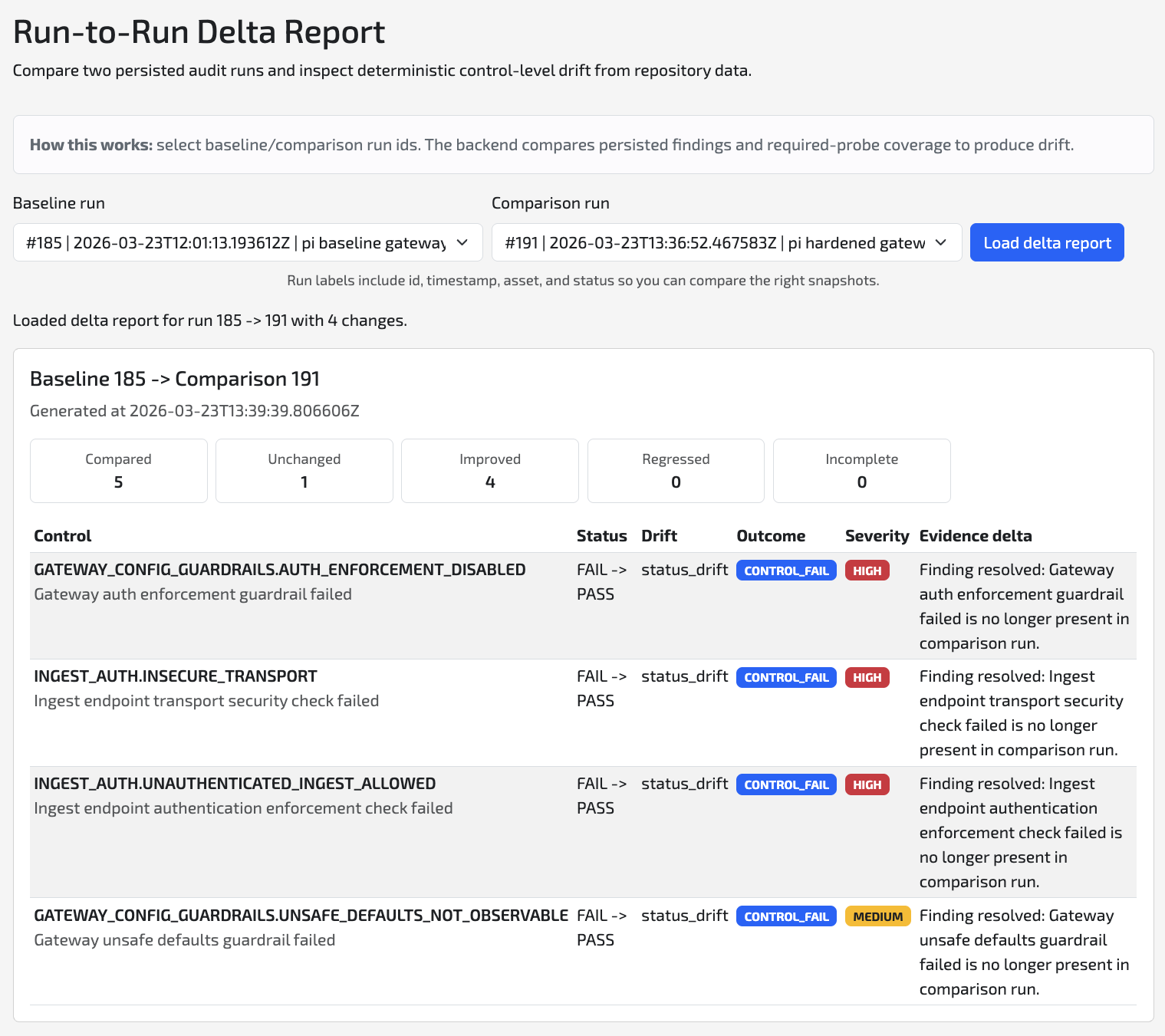
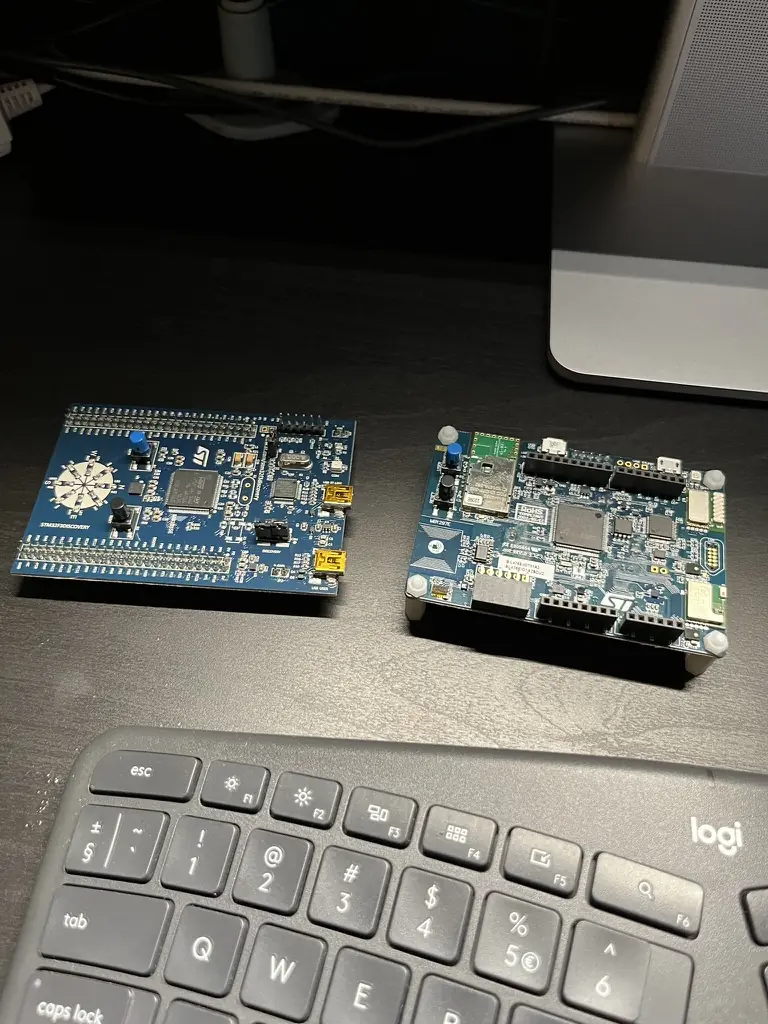
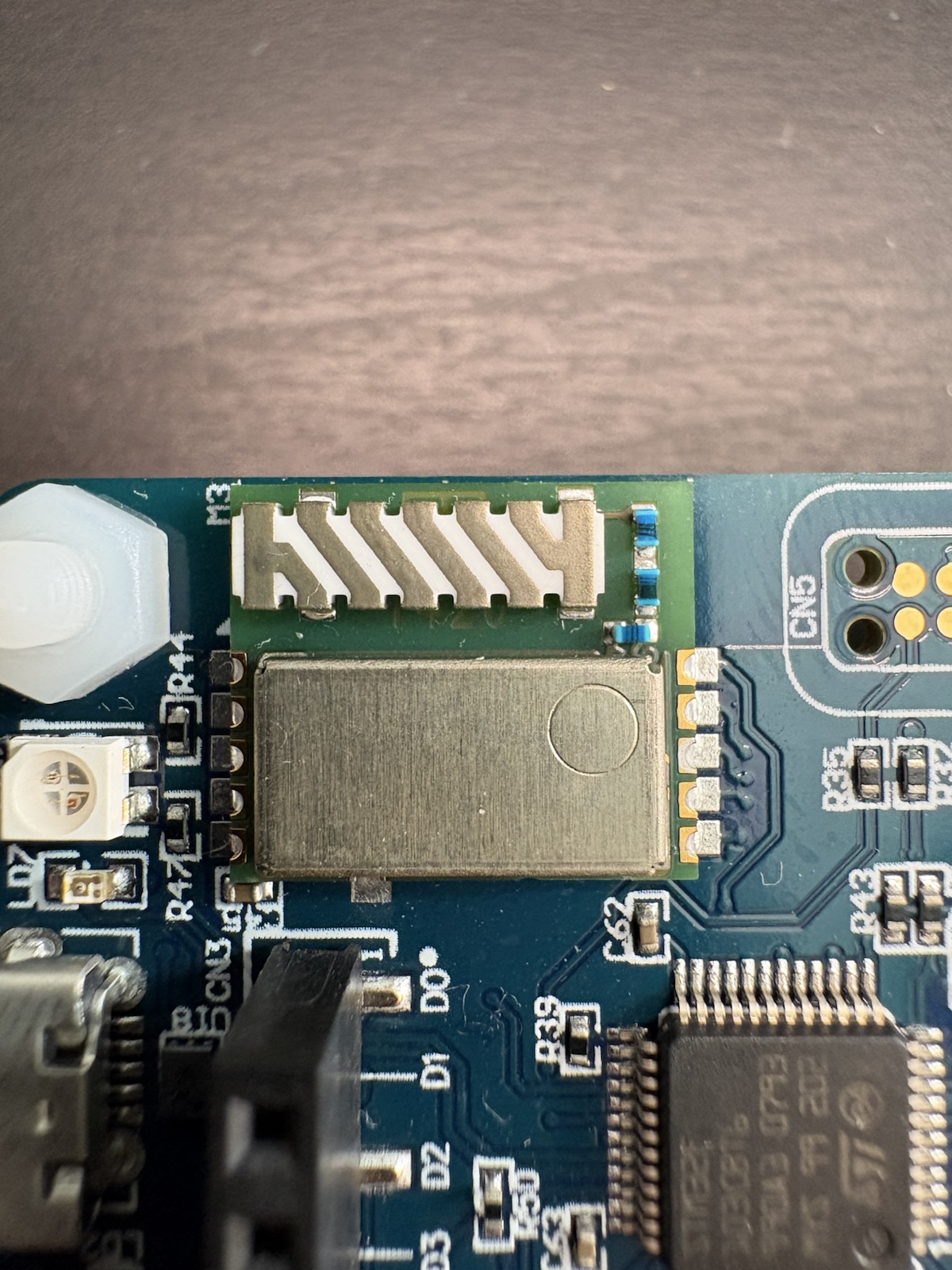
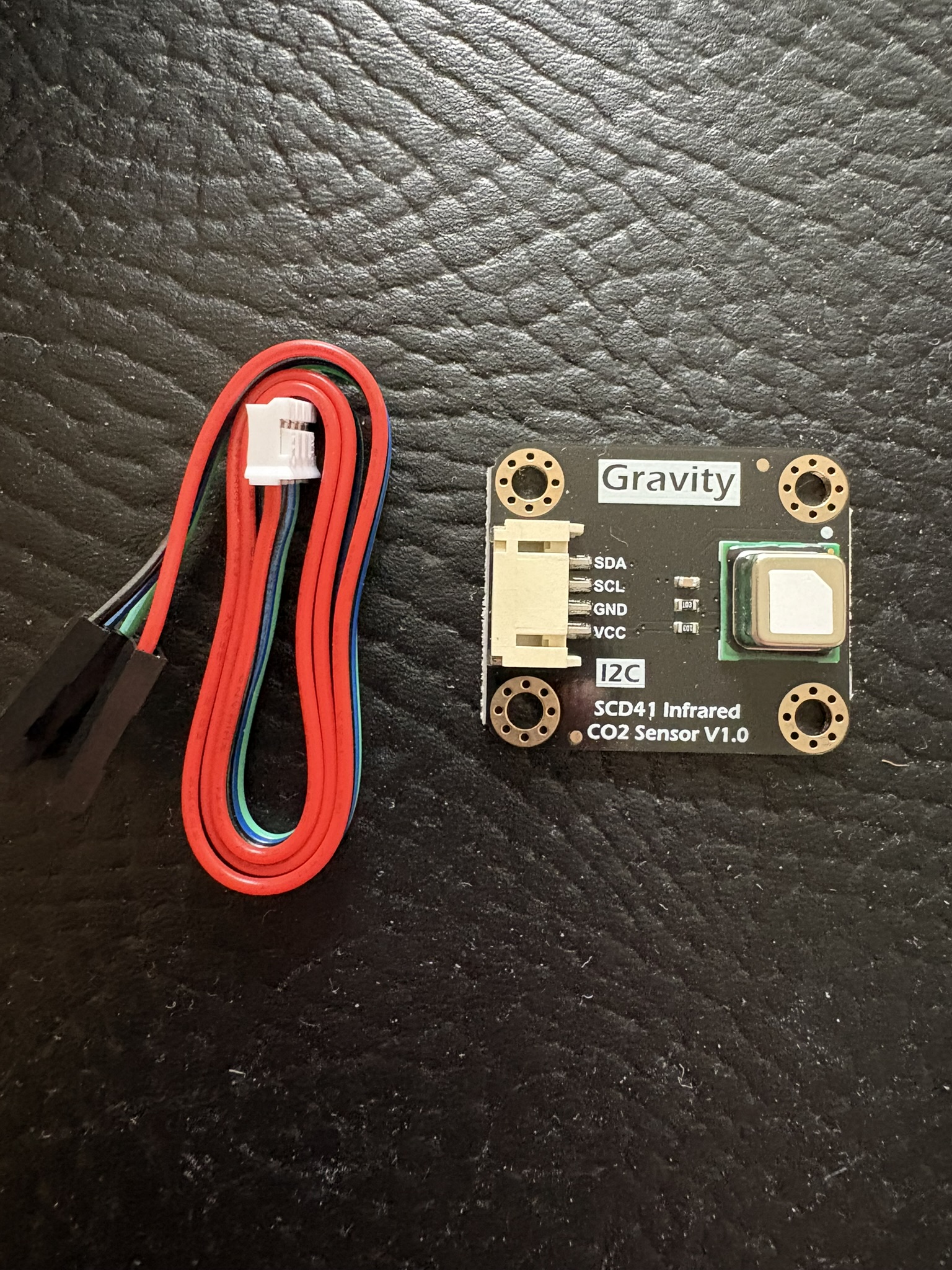
Engineering case study of integrating an SCD41 CO2 sensor with an STM32 B-L475E-IOT01A2 over I2C, publishing CO2, temperature, and humidity through MQTT with live room-state visibility and configurable CO2 alarms.